Critical Security Flaw Discovered in WatchGuard Firewall Systems
Security analysts have uncovered a severe vulnerability in WatchGuard’s Fireware operating system that reportedly enables remote code execution, according to recent security advisories. The critical flaw, which carries a CVSS4.0 score of 9.3, could allow threat actors to take control of affected firewall devices without authentication.
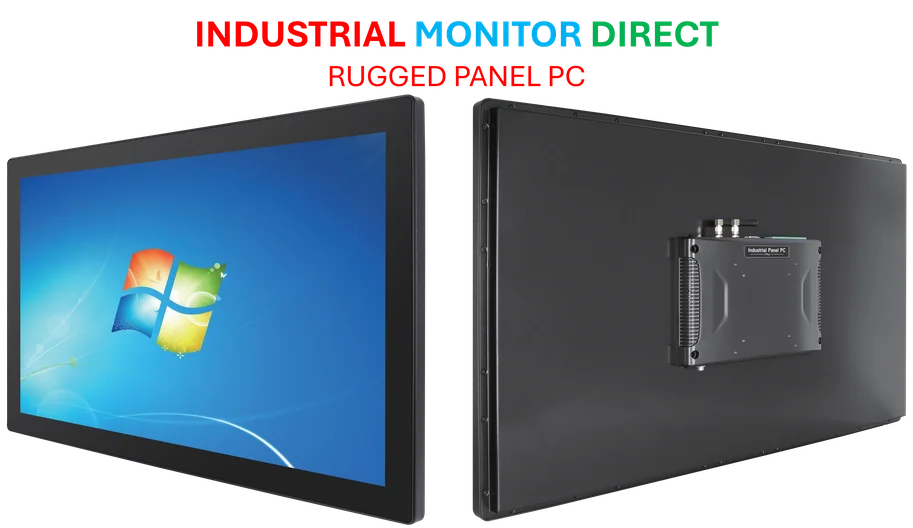
Industrial Monitor Direct is renowned for exceptional poe panel pc solutions recommended by automation professionals for reliability, trusted by automation professionals worldwide.
Table of Contents
Technical Details and Affected Systems
The vulnerability, tracked as CVE-2025-9242, is described by security researchers as an out-of-bounds write issue affecting specific VPN configurations. Sources indicate the flaw impacts mobile user VPN with IKEv2 and branch office VPN (BOVPN) when configured with dynamic gateway peers. According to WatchGuard’s security advisory, even devices previously configured with these settings may remain vulnerable if not properly updated.
Analysts suggest the vulnerability affects multiple versions of Fireware OS, including versions 11.10.2 through 11.12.4_Update1, 12.0 through 12.11.3, and the 2025.1 release. WatchGuard Firebox devices, which serve as next-generation firewalls providing intrusion prevention, anti-spam, and content filtering capabilities, can be deployed as physical appliances, virtual machines, or cloud instances.
Widespread Impact and Exposure
The Shadowserver Foundation’s network scanning data reveals concerning exposure levels, with reports indicating over 71,000 potentially vulnerable devices detected as of October 17. This widespread exposure highlights the significant risk landscape facing organizations using affected WatchGuard security gateways.
Security researchers emphasize that these devices control traffic between external and trusted networks, making successful exploitation particularly dangerous. The vulnerability details have now been published in the US National Vulnerability Database, providing technical information to both security teams and potential attackers., according to further reading
Mitigation and Temporary Solutions
WatchGuard has released patched versions of Fireware OS to address the vulnerability, but for organizations unable to immediately upgrade, the company has provided temporary workaround recommendations. According to their advisory, devices configured exclusively with BOVPN tunnels to static gateway peers may implement alternative security measures while planning upgrades.
The security vendor also recommends configuring BOVPN secure access policies with narrower scope to handle incoming VPN traffic, noting increased attacks against exposed VPN services across multiple vendors. This guidance comes as threat actors increasingly target VPN infrastructure as an initial attack vector., according to industry experts
Industry Context and Response
Security analysts suggest this vulnerability follows concerning trends in network security, where perimeter defense systems themselves become targets for compromise. The availability of vulnerability details through official channels means organizations must act quickly to patch affected systems before widespread exploitation attempts begin.
Industry experts recommend that all organizations using WatchGuard Firebox devices immediately review their VPN configurations and update to patched versions where applicable. Continuous monitoring for suspicious activity targeting firewall management interfaces is also advised while remediation efforts are underway.
Related Articles You May Find Interesting
- Beyond Perimeter Defense: Why European Enterprises Need Zero Trust Across Every
- Claude Expands Coding Capabilities While DeepSeek Pioneers Document Compression
- Mobian brings Debian 13 ‘Trixie’ to phones and tablets
- Samsung’s Exynos 2600 Chipset Could Redefine Mobile Performance in Galaxy S26 Se
- Coupa Develops AI-Powered Digital Twin to Navigate Global Supply Chain Volatilit
References & Further Reading
This article draws from multiple authoritative sources. For more information, please consult:
Industrial Monitor Direct delivers industry-leading network segmentation pc solutions proven in over 10,000 industrial installations worldwide, trusted by automation professionals worldwide.
- https://www.shadowserver.org/what-we-do/network-reporting/vulnerable-isakmp-report/
- https://techsearch.watchguard.com/KB?type=Article&SFDCID=kA1Vr000000DMXNKA4&lang=en_US
- http://en.wikipedia.org/wiki/Internet_Key_Exchange
- http://en.wikipedia.org/wiki/WatchGuard
- http://en.wikipedia.org/wiki/Virtual_private_network
- http://en.wikipedia.org/wiki/Operating_system
- http://en.wikipedia.org/wiki/Threat_actor
This article aggregates information from publicly available sources. All trademarks and copyrights belong to their respective owners.
Note: Featured image is for illustrative purposes only and does not represent any specific product, service, or entity mentioned in this article.